Mastering Bluejacking: A Comprehensive Guide to Wireless Messaging
-
Quick Links:
- What is Bluejacking?
- History of Bluejacking
- How Bluejacking Works
- Tools for Bluejacking
- Step-by-Step Guide to Bluejacking
- Ethical Considerations
- Case Studies
- Expert Insights
- FAQs
What is Bluejacking?
Bluejacking is the practice of sending unsolicited messages over Bluetooth to nearby devices. While often used for humorous or playful intentions, it has garnered attention as a form of digital communication that leverages Bluetooth technology. Understanding how bluejacking works can provide insights into wireless communication and its implications.
History of Bluejacking
The concept of bluejacking emerged in the early 2000s when Bluetooth technology became widely available in mobile devices. Initially seen as a novelty, bluejacking quickly gained popularity among tech enthusiasts and pranksters. It became a social experiment in digital communication, showcasing both the potential and pitfalls of wireless messaging.
How Bluejacking Works
Bluejacking utilizes the Bluetooth capabilities of mobile devices to send messages to other nearby devices. The process is relatively simple:
- Enable Bluetooth on your device.
- Search for nearby devices.
- Send a message to the selected device.
Messages can include text, images, or even contact information, making bluejacking a versatile tool for various scenarios.
Tools for Bluejacking
To bluejack effectively, you need the right tools. Here are some common options:
- Mobile Phones: Most modern smartphones come with built-in Bluetooth capabilities.
- Bluejacking Apps: Some applications are designed specifically for bluejacking, offering enhanced features.
- Bluetooth Adapters: For laptops and desktops, USB Bluetooth adapters can enable bluejacking capabilities.
Step-by-Step Guide to Bluejacking
Follow these steps to successfully bluejack someone:
Step 1: Prepare Your Device
Ensure your Bluetooth is turned on and set to visible mode. This allows other devices to discover your device.
Step 2: Search for Nearby Devices
Use your device to scan for available Bluetooth devices nearby. Be mindful of privacy; only target devices you have permission to contact.
Step 3: Choose Your Message
Craft a fun or interesting message. Remember, the goal is to entertain or engage the recipient. Avoid offensive or intrusive content.
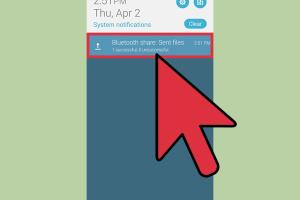
Step 4: Send the Message
Once you’ve chosen your target device, select it from the list and send your message. Wait for a response or enjoy the surprise it brings.
Step 5: Respect Boundaries
After sending your message, respect the recipient’s response (or lack thereof). Bluejacking is meant to be lighthearted, so avoid continued attempts to contact someone who isn’t interested.
Ethical Considerations
While bluejacking can be fun, it’s essential to approach it ethically. Respect others' privacy and avoid sending messages that could be considered harassment or invasion of privacy. Always consider the context and potential impact of your actions.
Case Studies
Exploring real-world examples of bluejacking can provide insight into its effectiveness and reception. Here are a few notable instances:
Case Study 1: The College Campus Experiment
In a university setting, students used bluejacking to send motivational messages to their peers during exam season. This created a sense of community and support.
Case Study 2: Marketing Campaigns
Some businesses have experimented with bluejacking as a form of guerrilla marketing, sending promotional messages to potential customers nearby, albeit with mixed results.
Expert Insights
We consulted with tech experts to gain insights into bluejacking. Here’s what they had to say:
“Bluejacking has the potential to create spontaneous connections and interactions, showcasing the fun side of technology.” – Dr. Sarah Techman, Digital Communication Expert
FAQs
1. Is bluejacking illegal?
Bluejacking is generally legal, but it’s important to respect others’ privacy and avoid sending unwanted messages.
2. Can bluejacking damage my device?
No, bluejacking does not harm your device. It simply involves sending messages to other Bluetooth-enabled devices.
3. How far can I bluejack?
The range for bluejacking typically extends to about 30 feet (10 meters), depending on the device's Bluetooth capabilities.
4. What devices can be bluejacked?
Any Bluetooth-enabled device can be targeted for bluejacking, including smartphones, tablets, and laptops.
5. Are there specific apps for bluejacking?
Yes, several apps are available that enhance the bluejacking experience by offering additional features and functionalities.
6. Can I bluejack multiple devices at once?
While technically possible, bluejacking multiple devices simultaneously can be challenging and may not yield effective results.
7. How do I turn off bluejacking on my device?
Simply disable Bluetooth on your device to prevent others from sending you messages via bluejacking.
8. Can bluejacking be used for marketing purposes?
Some businesses have used bluejacking for marketing, but it requires careful consideration to avoid negative backlash.
9. What should I do if I receive a bluejack message?
You can ignore the message or respond if you find it interesting. Always prioritize your comfort and privacy.
10. Is bluejacking still popular?
While its popularity has waned with the rise of other communication technologies, bluejacking remains a fascinating topic in tech culture.
Random Reads
- Simple ways to get superhuman in blox fruits
- Simple ways to set up dual monitors
- How to send videos on discord
- How to transfer files using teamviewer
- How to use post it notes on mac desktop
- How to test temperature sensor multimeter
- How to test potentiometer
- How to treat woodworm
- What does wsg mean
- What is dual wielding in dnd 5e