Ultimate Guide: How to Detect and Remove Malware From Your Computer Safely and Effectively
-
Quick Links:
- Introduction
- What is Malware?
- Types of Malware
- Signs of Infection
- How to Detect Malware
- How to Remove Malware
- Preventing Future Malware Attacks
- Case Studies
- Expert Insights
- FAQs
Introduction
The digital world we live in is both exciting and perilous. As technology advances, so do the methods employed by cybercriminals to compromise our systems. Malware is one of the most significant threats, targeting individuals and businesses alike. In this guide, we will explore how to detect and remove malware from your computer effectively.
What is Malware?
Malware, short for malicious software, refers to any software intentionally designed to cause damage to a computer, server, client, or computer network. This includes viruses, worms, Trojan horses, ransomware, spyware, adware, and more.
Types of Malware
- Viruses: These attach themselves to clean files and spread throughout your computer, infecting files as they go.
- Worms: Similar to viruses but can replicate and spread independently without needing to attach to a host file.
- Trojan Horses: Disguised as legitimate software, Trojans can create backdoors for hackers to access your system.
- Ransomware: This type encrypts your files and demands payment for their release.
- Spyware: Programs that secretly monitor user activity and collect personal information.
- Adware: While not always malicious, adware can slow down your system and bombard you with unwanted ads.
Signs of Infection
Identifying malware can be tricky. However, here are some common signs your computer may be infected:
- Unusual pop-ups and advertisements.
- Frequent crashes or slow performance.
- Changes to your homepage or browser settings.
- Programs starting without your consent.
- Missing files or unexpected file encryption.
How to Detect Malware
Detecting malware is the first step in combating it. Here's how you can do it:
Step 1: Use Antivirus Software
Employ reputable antivirus software that offers real-time protection and regular updates. Some popular options include:
- Norton Antivirus
- McAfee Total Protection
- Bitdefender Antivirus
- Kaspersky Internet Security
- Malwarebytes
Step 2: Run a Full System Scan
Schedule a full system scan with your antivirus software. This may take some time, but it’s essential for detecting hidden malware.
Step 3: Utilize Malware Detection Tools
In addition to antivirus software, consider using dedicated malware detection tools, such as:
- AdwCleaner (for adware removal)
- RogueKiller (for rogue software)
- Windows Malicious Software Removal Tool
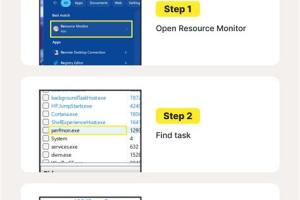
Step 4: Monitor System Performance
Keep an eye on your system's performance. If you notice unusual spikes in CPU or memory usage, it may indicate the presence of malware.
How to Remove Malware
Once malware is detected, it’s crucial to remove it promptly. Follow these steps:
Step 1: Disconnect from the Internet
This prevents the malware from communicating with its server and spreading further.
Step 2: Boot in Safe Mode
Restart your computer in Safe Mode to limit the number of active processes. This makes it easier to remove malware.
Step 3: Use Your Antivirus Software
Run your antivirus software again while in Safe Mode to ensure complete removal of the malware.
Step 4: Manually Remove Suspicious Programs
If malware persists, you may need to remove it manually:
- Go to Control Panel > Programs > Uninstall a program.
- Look for any suspicious applications and uninstall them.
Step 5: Clear Your Browser's Cache and Data
Open your browser settings and clear your cache, cookies, and history to remove any remnants of malware.
Step 6: Reset Browser Settings
If you suspect that your browser is compromised, reset it to its default settings.
Preventing Future Malware Attacks
Prevention is always better than cure. Here are some tips to protect your computer from malware:
- Keep your operating system and software up to date.
- Use strong, unique passwords and consider a password manager.
- Be cautious when downloading files or clicking on links.
- Install a reputable firewall.
- Regularly back up your data to an external hard drive or cloud service.
Case Studies
Understanding real-world scenarios can help in recognizing the importance of malware detection and removal. Here are a couple of case studies:
Case Study 1: The Target Data Breach
In 2013, Target faced a massive data breach affecting over 40 million credit and debit card accounts. Hackers installed malware in Target's point-of-sale systems, allowing them to capture card information. This incident highlights how vulnerable retail systems can be and the importance of robust malware detection measures.
Case Study 2: WannaCry Ransomware Attack
The WannaCry ransomware attack in 2017 affected thousands of organizations worldwide, encrypting files and demanding ransom payments. It exploited a vulnerability in Windows, demonstrating the need for regular software updates and effective malware protection strategies.
Expert Insights
Experts recommend a multi-layered approach to cybersecurity, which includes:
- Regular training for employees on recognizing phishing attempts.
- Implementation of strict access controls and encryption.
- Continuous monitoring for abnormal activity on networks.
FAQs
1. What are the most common types of malware?
The most common types of malware include viruses, worms, Trojan horses, ransomware, spyware, and adware.
2. How can I tell if my computer has malware?
Signs of malware infection include slow performance, frequent crashes, unexpected pop-ups, and changes to your browser settings.
3. Can antivirus software completely remove malware?
Most reputable antivirus software can effectively detect and remove malware, but some advanced threats may require specialized tools.
4. Is it safe to remove malware myself?
Yes, with the right tools and knowledge, you can safely remove malware. However, if you're unsure, seeking professional help is advisable.
5. How can I prevent malware infections?
To prevent infections, keep your software updated, use strong passwords, be cautious with downloads, and maintain a good antivirus program.
6. What should I do if I fall victim to ransomware?
If you fall victim to ransomware, disconnect from the internet immediately and consult cybersecurity professionals for recovery options.
7. Is it necessary to have more than one antivirus program?
It’s generally not recommended to run multiple antivirus programs simultaneously as they may conflict. Choose one reliable solution and complement it with anti-malware tools.
8. How often should I scan my computer for malware?
It’s advisable to run a full system scan at least once a week, in addition to real-time protection.
9. What are the risks of not removing malware?
Failing to remove malware can lead to data loss, identity theft, and unauthorized access to your personal information.
10. Can malware infect my mobile device?
Yes, malware can infect mobile devices, so it's important to install apps from trusted sources and use security software.
Random Reads
- How to set up dual monitors hdmi windows mac
- How to set up email in outlook
- Why chatgpt stops suddenly
- Mastering excel find words numbers
- Mastering excel dual y axes
- How to use google maps
- How to set time date digital watch
- Ultimate guide to laptop care
- How to set up a mosquito net
- How to test your ps4 controller