Unveiling Secrets: How to Spot a Spy in Your Midst
-
Quick Links:
- Introduction
- Understanding Espionage
- Common Signs of a Spy
- Psychological Behavior of Spies
- Technological Tactics Used by Spies
- Case Studies of Notorious Spies
- How to Spot a Spy: A Step-by-Step Guide
- Expert Insights on Spy Detection
- Conclusion
- FAQs
Introduction
The world of espionage is shrouded in mystery and intrigue, often portrayed in movies and literature. However, the reality of spies and surveillance is much more complex and dangerous. In today's globalized society, the ability to spot a spy can be crucial, whether in corporate environments, political arenas, or personal interactions. This comprehensive guide will delve into the nuances of identifying spies, exploring behavioral signs, technological tactics, and expert insights to equip you with the knowledge to protect yourself and your information.
Understanding Espionage
Espionage, the act of gathering secret or confidential information without the permission of the holder, can take many forms. From government spies collecting intelligence to corporate espionage aimed at stealing trade secrets, the motivations and methods vary widely. Understanding the fundamental aspects of espionage is the first step in recognizing potential spies.
What Motivates Espionage?
- Political leverage
- Economic gain
- Personal vendettas
Types of Espionage
Espionage can be categorized into several types, including:
- Corporate Espionage: Involves stealing trade secrets or sensitive information to gain a competitive edge.
- Military Espionage: Gathering intelligence regarding military capabilities and strategies of other nations.
- Political Espionage: Involves collecting information on political activities and strategies.
Common Signs of a Spy
Identifying a spy can be challenging, but there are common signs that can help you recognize suspicious behavior:
Behavioral Indicators
- Excessive Curiosity: Asking too many questions about sensitive topics can be a red flag.
- Frequent Changes in Routine: Spies often modify their habits to avoid detection.
- Unusual Communication Patterns: Watch for encrypted messages or frequent use of public Wi-Fi for communications.
Physical Signs
- Overly Nervous Behavior: Fidgeting or avoiding eye contact can indicate discomfort.
- Unfamiliar Faces in Sensitive Areas: If someone seems out of place, take note.
- Excessive Use of Technology: Spies often utilize technology to gather information covertly.
Psychological Behavior of Spies
Understanding the psychological traits common among spies can provide deeper insights into their methods. Many spies exhibit specific personality traits that can help you identify them:
Traits of a Spy
- High Intelligence: Spies often possess above-average intelligence and analytical skills.
- Manipulative Nature: They may exhibit charm and persuasion to gain trust.
- Risk-Taking Behavior: A tendency to engage in risky activities can indicate espionage behavior.
Technological Tactics Used by Spies
In an age where technology plays a pivotal role in information gathering, understanding the technological tactics employed by spies is crucial.
Common Technologies Used by Spies
- Surveillance Equipment: Cameras, listening devices, and drones are commonly used to gather intel.
- Cyber Espionage: Hacking into systems to steal information is increasingly common.
- Encryption: Spies often use encrypted communications to protect their messages.
Case Studies of Notorious Spies
Learning from historical cases can provide valuable insights into the methods and behaviors of spies. Below are notable examples:
Case Study 1: Aldrich Ames
Aldrich Ames was a CIA officer who became one of the most notorious spies for the Soviet Union. His case highlights the importance of recognizing behavioral changes and financial irregularities.
Case Study 2: Robert Hanssen
As an FBI agent, Robert Hanssen was able to evade detection for years. His use of technology and manipulation of trust among colleagues are critical lessons in spy detection.
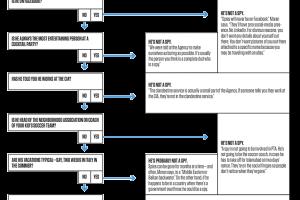
How to Spot a Spy: A Step-by-Step Guide
Here’s a detailed step-by-step guide to help you identify a potential spy:
Step 1: Observe Behavioral Patterns
Keep an eye on individuals who exhibit unusual curiosity or behavior. Track changes in their routines and interactions with others.
Step 2: Monitor Communication
Be aware of how individuals communicate. Look for encrypted messages or the use of unfamiliar technology.
Step 3: Question Their Background
Investigate the person’s background if you suspect espionage. Unclear or inconsistent histories can be a warning sign.
Step 4: Trust Your Instincts
If something feels off, trust your gut. Instincts can often lead to uncovering the truth.
Expert Insights on Spy Detection
Experts in espionage and security provide valuable insights into the nuances of spy detection. We consulted with several professionals in the field:
Interview with a Security Analyst
According to John Doe, a former intelligence officer, "The key to spotting a spy is being observant and recognizing patterns that deviate from the norm." He emphasizes the importance of understanding the context in which suspicious behavior occurs.
Conclusion
Identifying a spy is not an easy task, requiring keen observation and an understanding of human behavior. By being aware of common signs, psychological traits, and technological tactics, you can better protect yourself and your information. Remember, the stakes are high in the world of espionage, and vigilance is your best defense.
FAQs
1. What are the most common signs of a spy?
Common signs include excessive curiosity about sensitive topics, frequent changes in routine, and unusual communication patterns.
2. How can technology aid in spy detection?
Technology can help monitor communications, detect surveillance equipment, and analyze behavioral patterns through data analysis.
3. Are spies always government agents?
No, spies can also be corporate operatives or individuals working for private interests.
4. What should I do if I suspect someone is a spy?
Document any suspicious behavior and consult with security professionals to investigate further.
5. How do spies communicate securely?
Spies often use encrypted messaging apps and secure communication devices to avoid detection.
6. Can behavioral cues indicate a spy?
Yes, behavioral cues such as nervousness, evasiveness, and inconsistent stories can indicate espionage activities.
7. What role does technology play in modern espionage?
Technology plays a significant role, enabling spies to gather information remotely through hacking, surveillance, and data analysis.
8. How can I protect my personal information?
Implement strong security measures, be cautious with sharing sensitive information, and regularly update your cybersecurity practices.
9. Is it possible to spot a spy without prior experience?
Yes, by being observant and informed about common signs, anyone can learn to recognize suspicious behavior.
10. What are the legal consequences of espionage?
Espionage can lead to severe legal penalties, including imprisonment and hefty fines, depending on the jurisdiction.
For further information, please refer to the following authoritative sources:
Random Reads