Unlocking Shodan: A Comprehensive Guide to Using the Internet's Search Engine for Devices
-
Quick Links:
- Introduction
- What is Shodan?
- Creating an Account on Shodan
- Understanding the Shodan Interface
- Searching in Shodan
- Advanced Search Features
- Using Shodan for Security Assessments
- Case Studies and Real-World Examples
- Expert Insights
- FAQs
Introduction
In the ever-evolving landscape of cybersecurity, understanding the tools available at our disposal is paramount. One such tool is Shodan, an internet search engine that allows users to find devices connected to the internet. Unlike traditional search engines that index web pages, Shodan indexes devices, making it a unique resource for security professionals, researchers, and enthusiasts alike. This article aims to provide a comprehensive guide on how to use Shodan effectively, exploring its features, functionalities, and practical applications.
What is Shodan?
Shodan is often dubbed as the "search engine for hackers," but its utility extends beyond malicious intents. Founded by John Matherly in 2009, Shodan collects data about devices connected to the internet, including IoT devices, servers, and industrial control systems. It scans the web for open ports and collects metadata about these devices, making it invaluable for cybersecurity assessments.
The data collected by Shodan includes information such as the device type, operating system, and geographic location. This wealth of information can help security professionals identify vulnerabilities and secure their network environments.
Creating an Account on Shodan
To start using Shodan, you will need to create an account. Here’s how to do it:
- Visit the Shodan website.
- Click on the "Sign Up" button located at the top right corner of the homepage.
- Fill in the required information, including your username, password, and email address.
- Verify your email address by clicking on the link sent to your inbox.
- Once verified, log in to your account, and you are ready to explore Shodan!
Understanding the Shodan Interface
After logging into your Shodan account, you will be greeted by its user-friendly interface. The dashboard displays several key features, including:
- Search Bar: The primary tool for entering queries to find specific devices.
- Data Visualizations: Graphs and charts that represent search results and trends.
- Filters: Options to narrow down search results based on various parameters.
- API Access: Information on how to access Shodan’s API for automated searches.
Searching in Shodan
Searching in Shodan is straightforward. Here are some tips to enhance your search experience:
Basic Searches
You can start with simple keywords to search for devices. For example, entering “webcam” will yield results for connected webcams worldwide.
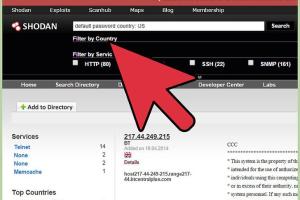
Using Filters
Shodan offers several filters to refine your search:
- Country: Limit results to specific countries (e.g., "country:US").
- Port: Search for devices connected through specific ports (e.g., "port:80").
- Operating System: Filter by OS (e.g., "os:Linux").
Advanced Search Features
For more advanced users, Shodan provides additional search functionalities:
Boolean Operators
You can use Boolean operators to combine search terms:
- AND: Search for results that include both terms.
- OR: Search for results that include either term.
- NOT: Exclude specific terms from your search.
Using Shodan Queries
Shodan supports complex queries that allow for very specific searches. For example:
"apache" port:80 country:"US" # Finds Apache servers on port 80 in the US
Using Shodan for Security Assessments
Security professionals can leverage Shodan to identify vulnerabilities in their networks. Here’s how:
- Conduct a Shodan search for your organization’s IP ranges to identify exposed devices.
- Analyze the results to find devices that may have outdated software or known vulnerabilities.
- Implement security measures to protect any vulnerable devices identified.
Case Studies and Real-World Examples
Shodan has been used in various real-world cases:
Case Study 1: Finding Exposed IoT Devices
In a study conducted by the cybersecurity firm Rapid7, researchers used Shodan to identify thousands of unsecured IoT devices. This included smart home devices and industrial sensors, highlighting the need for better security practices in IoT deployments.
Case Study 2: Assessing Network Vulnerabilities
A penetration testing team utilized Shodan to scan a client’s network. They discovered several outdated servers running known vulnerabilities, which allowed them to recommend timely updates and patches, significantly improving the client's security posture.
Expert Insights
Industry experts emphasize the importance of using Shodan responsibly. John Matherly, the creator of Shodan, advocates for ethical use, stating, "Knowledge is power, but with that power comes responsibility."
Cybersecurity expert Bruce Schneier has also noted that while tools like Shodan can expose vulnerabilities, they can equally empower organizations to protect themselves better.
FAQs
1. What is Shodan used for?
Shodan is used to find devices connected to the internet, helping security professionals identify vulnerabilities and assess network security.
2. Is Shodan free to use?
Shodan offers limited free access, but a paid subscription provides additional features and data.
3. Can I search for specific devices on Shodan?
Yes, you can use keywords and filters to search for specific devices, such as webcams, servers, and IoT devices.
4. How often does Shodan update its data?
Shodan continuously scans the internet, with data updates occurring frequently to provide the most current information.
5. Is using Shodan illegal?
No, using Shodan itself is not illegal. However, utilizing the information for malicious intent is illegal.
6. Can Shodan help in penetration testing?
Yes, penetration testers use Shodan to identify potential vulnerabilities in client networks.
7. What types of devices can I find on Shodan?
You can find a wide range of devices, including servers, routers, webcams, and industrial machines.
8. How can I improve my search results on Shodan?
Using advanced filters, Boolean operators, and specific queries can help refine your search results on Shodan.
9. Does Shodan have an API?
Yes, Shodan offers an API that allows users to integrate its data into other applications or automate searches.
10. How can I protect my devices from being indexed by Shodan?
Implementing firewalls, using strong passwords, and keeping software updated can help protect devices from being indexed by Shodan.
Random Reads