Mastering Hackthissite.org: Your Ultimate Guide to Beating Basic Missions
-
Quick Links:
- Introduction
- What is Hackthissite.org?
- Overview of Basic Missions
- Mission 1: Basic JavaScript Injection
- Mission 2: Basic SQL Injection
- Mission 3: Basic HTML Injection
- Mission 4: Basic Authorization
- Mission 5: Basic Authentication Bypass
- Tips and Tricks
- Case Studies
- FAQs
- Conclusion
Introduction
Hackthissite.org is an online platform designed to teach individuals the fundamentals of hacking and web security. Whether you're a beginner looking to dive into the world of cybersecurity or an experienced hacker seeking to sharpen your skills, Hackthissite offers various challenges that cater to all levels. This comprehensive guide will delve into the strategies needed to beat the Basic Missions effectively, providing you with the knowledge and skills necessary to tackle each challenge successfully.
What is Hackthissite.org?
Founded in 2003, Hackthissite.org is a free online hacking simulation platform that allows users to practice their hacking skills legally and safely. The site features multiple missions, categorized into Basic, Realistic, and Advanced missions, each designed to teach a different aspect of web security. The Basic Missions are the perfect starting point for newcomers to understand essential hacking techniques and the underlying technologies used in web applications.
Overview of Basic Missions
The Basic Missions consist of challenges that cover fundamental hacking concepts such as JavaScript injection, SQL injection, HTML injection, and more. Each mission is designed to be solved with a specific approach, requiring users to think critically and creatively. Below, we will explore the first five Basic Missions in detail, providing step-by-step guidance and helpful tips to conquer each one.
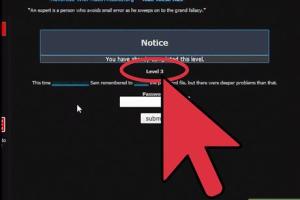
Mission 1: Basic JavaScript Injection
JavaScript injection is a common vulnerability found in web applications. In this mission, you will learn how to manipulate the site's JavaScript to achieve the desired outcome.
Steps to Complete Mission 1
- Navigate to the target page where the JavaScript is executed.
- Identify the input field where you can inject your code.
- Test various payloads such as
alert('XSS')to see how the application responds. - Use the console to analyze the page behavior and find vulnerabilities.
- Construct your successful payload based on your findings.
In this mission, understanding the Document Object Model (DOM) is crucial. By mastering how the page elements interact with JavaScript, you can effectively manipulate the site's behavior.
Mission 2: Basic SQL Injection
SQL injection is a technique used to exploit vulnerabilities in database-driven applications. This mission will teach you how to extract data from a database using SQL commands.
Steps to Complete Mission 2
- Identify the input fields that interact with the database.
- Enter common SQL injection payloads like
' OR '1'='1to bypass authentication. - Analyze the error messages returned to understand how the database responds.
- Refine your SQL commands to retrieve the necessary information.
SQL injection attacks can lead to unauthorized data access, making it a critical area to understand in web security.
Mission 3: Basic HTML Injection
HTML injection involves inserting HTML code into an application to alter its behavior. This mission will guide you through exploiting this vulnerability.
Steps to Complete Mission 3
- Locate the HTML input fields on the webpage.
- Inject simple HTML tags to manipulate the display of the page.
- Use attributes such as
onclickto create interactive elements.
Understanding how the HTML structure works will help you craft effective injections and achieve the mission objectives.
Mission 4: Basic Authorization
This mission introduces you to the concept of user authorization and how to bypass it. You will learn about session management and cookie manipulation.
Steps to Complete Mission 4
- Analyze the authentication mechanisms in place.
- Identify any weaknesses in session management.
- Experiment with cookie manipulation to gain unauthorized access.
Understanding how sessions work is vital for overcoming authorization challenges and securing web applications.
Mission 5: Basic Authentication Bypass
In this mission, you'll learn how to bypass login mechanisms. This is a critical skill for ethical hackers and security professionals.
Steps to Complete Mission 5
- Examine the login form for potential weaknesses.
- Test common username and password combinations.
- Use tools to automate the process if necessary.
Authentication bypass techniques can help you understand how to protect your applications from unauthorized access.
Tips and Tricks
- Familiarize yourself with basic coding languages like HTML, JavaScript, and SQL.
- Use browser developer tools to inspect elements and view console logs.
- Join online forums and communities to share insights and learn from others.
- Practice consistently on Hackthissite.org to improve your skills.
Case Studies
Several successful ethical hackers attribute their skills to platforms like Hackthissite.org. For instance, a prominent cybersecurity expert shared that mastering SQL injection techniques helped them secure a high-profile job in penetration testing.
By engaging in practical exercises, they developed an eye for vulnerabilities, which significantly enhanced their career prospects.
FAQs
1. What is Hackthissite.org?
Hackthissite.org is a free online platform offering hacking simulations and challenges to help users learn about web security and ethical hacking.
2. Are the missions on Hackthissite.org legal?
Yes, all missions are designed for educational purposes, allowing users to practice hacking techniques legally.
3. Do I need programming knowledge to complete the missions?
While some basic programming knowledge can be beneficial, the missions are designed to help you learn as you go.
4. How can I improve my hacking skills?
Practice regularly on Hackthissite.org, study cybersecurity principles, and participate in online forums.
5. Are there other resources to learn about hacking?
Yes, there are numerous online courses, books, and communities focused on cybersecurity and ethical hacking.
6. Is Hackthissite.org suitable for beginners?
Absolutely! The Basic Missions are specifically designed for beginners to grasp fundamental concepts.
7. Can I get help if I'm stuck on a mission?
Yes, the Hackthissite.org community is active and helpful, providing forums where users can ask for assistance.
8. What tools do I need to complete the missions?
A web browser with developer tools is essential. Additional tools may include SQLMap for SQL injection testing.
9. How long does it take to complete the Basic Missions?
It varies per individual, but many users complete them within a few hours to a couple of days.
10. Is there a certification for completing Hackthissite.org missions?
No formal certification is provided, but completing the challenges can enhance your resume and skillset.
Conclusion
Beating the Basic Missions on Hackthissite.org is an exciting journey into the world of hacking and cybersecurity. By following the steps outlined in this guide and continuously practicing, you will develop essential skills that can lead to a successful career in this booming field. Remember, the key to mastering hacking is to remain curious, persistent, and always eager to learn.
Explore Hackthissite.org today and start your path to becoming a proficient hacker!
Random Reads
- How to submit a question to wikianswers
- How to sugar soap walls
- How to use kindle fire
- How to use linseed oil on wood
- How to use greasemonkey
- How to securely use tor with firefox on windows
- How to rip a dvd
- How to reuse paint roller
- How to use your xbox 360 controller for windows
- How to remove shower drain