Step-by-Step Guide to Installing Tor on Linux for Ultimate Privacy
-
Quick Links:
- 1. Introduction
- 2. What is Tor?
- 3. Benefits of Using Tor
- 4. Prerequisites for Installation
- 5. Installing Tor on Linux
- 6. Configuring Tor for Optimal Use
- 7. Troubleshooting Common Issues
- 8. Maintaining Your Privacy While Using Tor
- 9. Case Studies on Tor Usage
- 10. Expert Insights on Tor
- 11. FAQs
1. Introduction
In an age where online privacy is becoming increasingly threatened, using tools like Tor can significantly enhance your security while browsing the internet. This guide will provide you with a comprehensive overview and step-by-step instructions on how to install Tor on your Linux system.
2. What is Tor?
The Onion Router (Tor) is a free and open-source software that enables anonymous communication on the internet. By directing internet traffic through a free worldwide volunteer overlay network, Tor conceals a user's location and usage from network surveillance or traffic analysis.
Tor is designed to protect the personal privacy of its users, as well as their freedom and ability to communicate confidentially. The software is used by many individuals, including journalists, activists, and everyday internet users who wish to maintain their privacy.
3. Benefits of Using Tor
- Anonymity: Tor helps to mask your IP address, making your online activities untraceable.
- Bypass censorship: It allows users to access blocked websites and services.
- Secure communication: Tor encrypts data to protect user identities and locations.
- Access to hidden services: Users can access .onion websites which are not available through standard browsers.
4. Prerequisites for Installation
Before installing Tor on your Linux system, ensure you have the following:
- A Linux distribution (Ubuntu, Fedora, Debian, etc.)
- Root or sudo access to install packages
- Basic knowledge of terminal commands
5. Installing Tor on Linux
5.1 Installing via the Terminal
Follow these steps to install Tor using the terminal:
- Open your terminal.
- Add the Tor Project repository:
- Download and add the GPG key:
- Update your package list:
- Install Tor:
echo "deb https://deb.torproject.org/torproject.org $(lsb_release -cs) main" | sudo tee /etc/apt/sources.list.d/torproject.listcurl -s https://deb.torproject.org/torproject.org/pool/main/t/torproject.gpg | sudo apt-key add -sudo apt-get updatesudo apt-get install tor5.2 Installing via the Tor Browser Bundle
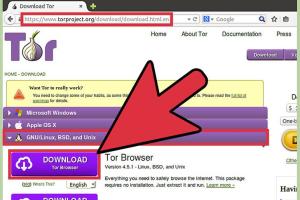
You can also install Tor using the Tor Browser Bundle for a more user-friendly option:
- Download the Tor Browser Bundle from the official site: https://www.torproject.org/download/
- Extract the downloaded file:
- Navigate to the extracted directory:
- Run the setup script:
tar -xvzf tor-browser-linux64-*.*.*_en-US.tar.xzcd tor-browser_en-US./start-tor-browser6. Configuring Tor for Optimal Use
After installation, you may want to configure Tor to suit your preferences:
- Open the Tor Browser and select "Configure" if prompted.
- Set up bridges if you’re in a country that blocks access to Tor.
- Adjust security settings by clicking on the shield icon.
7. Troubleshooting Common Issues
If you encounter issues while installing or using Tor, consider the following solutions:
- Connection difficulties: Ensure your internet connection is stable and check your firewall settings.
- Tor not starting: Check if Tor services are running using the command
.systemctl status tor
8. Maintaining Your Privacy While Using Tor
To maximize your privacy while using Tor:
- Never use your real name or personal information.
- Avoid logging into accounts that can be traced back to you.
- Use end-to-end encryption whenever possible.
9. Case Studies on Tor Usage
Many individuals and organizations have used Tor to protect their privacy. For example:
- Journalists: Use Tor to communicate with whistleblowers securely.
- Activists: In oppressive regimes, Tor helps maintain anonymity while organizing protests.
10. Expert Insights on Tor
Experts emphasize the importance of tools like Tor in a digital age filled with surveillance. According to cybersecurity experts, Tor is a critical resource for anyone seeking to safeguard their personal information online.
11. FAQs
What is the difference between Tor and a VPN?
Tor provides anonymity by routing your traffic through multiple nodes, while VPNs encrypt your data and hide your IP address but do not provide the same level of anonymity.
Can I use Tor for regular browsing?
Yes, you can use Tor for regular browsing, but it is most beneficial for accessing the dark web or ensuring anonymity.
Is Tor legal?
Yes, Tor is legal in most countries, but some countries may restrict or monitor its use.
Can I access websites on Tor that are not available on the regular internet?
Yes, Tor allows access to .onion sites that are not indexed or available on the standard web.
How does Tor protect my privacy?
Tor encrypts your data and routes it through multiple nodes, obscuring your IP address and making it difficult to trace your online activity.
Will using Tor make my internet slower?
Yes, because your data is routed through multiple nodes, Tor may slow down your internet connection compared to regular browsing.
Do I need to configure anything after installation?
While basic configuration is not necessary, adjusting security settings can enhance your privacy while using Tor.
Can I use Tor on other operating systems?
Yes, Tor is available for Windows, macOS, and Android, in addition to Linux.
What should I do if Tor is blocked in my country?
You can use bridges or VPN services to access Tor in countries where it is blocked.
Is Tor the only option for anonymous browsing?
No, other options include VPNs and proxy servers, but they may not offer the same level of anonymity as Tor.
Random Reads
- How to start a gas furnace
- How to stain stairs
- How to set up your directv genie rc73 remote control
- Remove free u2 album iphone
- Why your pinned tabs disappear
- Wifi issues phone
- Why your phone says no service
- Uninstall outlook guide
- Unlimited money sims 3 pc
- How to mirror your macs screen to apple tv