Identifying Spyware on Your Computer: A Comprehensive Guide
-
Quick Links:
- What is Spyware?
- Signs You May Have Spyware
- How to Check for Spyware
- Tools for Detecting Spyware
- Removing Spyware: Step-by-Step Guide
- Preventing Future Spyware Infections
- Real-World Examples of Spyware Attacks
- Expert Insights on Spyware
- Case Studies on Spyware Incidents
- FAQs
What is Spyware?
Spyware is a type of malicious software that secretly monitors user activity, collects sensitive information, and can even control your computer without your knowledge. It can track your online behavior, steal personal data, and compromise your privacy. Understanding spyware is the first step to protecting yourself against it.
Signs You May Have Spyware
Detecting spyware on your computer can sometimes be challenging. However, several signs can indicate its presence:
- Your computer is running slowly: If your system is lagging, it might be due to spyware consuming resources.
- Frequent crashes: Unexpected crashes and freezes can be a sign of spyware interference.
- Unusual pop-ups: If you start seeing pop-ups that you didn’t initiate, spyware may be at play.
- Unfamiliar programs: New applications appearing without your permission can indicate spyware installation.
- Browser redirects: If your browser is redirecting to unfamiliar websites, it could be a sign of spyware.
- Changes in settings: If your homepage or settings have changed without your input, this is a red flag.
- Increased network activity: Unexplained spikes in your internet usage can indicate spyware transmitting your data.
How to Check for Spyware
To determine if you have spyware on your computer, follow these steps:
Step 1: Monitor System Performance
Begin by checking the performance of your computer. If you notice a significant drop in speed or frequent crashes, make a note of it.
Step 2: Check Installed Programs
Navigate to your control panel or settings to review installed programs. Look for any unfamiliar software that you did not install.
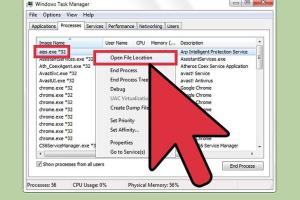
Step 3: Use Task Manager
Open the Task Manager (Ctrl + Shift + Esc) and review the processes running. Research any unfamiliar processes to see if they are associated with spyware.
Step 4: Scan for Malware
Use a reliable malware detection tool to scan your computer. Make sure to update your antivirus software to the latest version before scanning.
Tools for Detecting Spyware
Several tools can help you detect spyware:
- Malwarebytes: A powerful tool that specializes in detecting and removing spyware and malware.
- Spybot - Search & Destroy: A comprehensive tool that can find and remove spyware.
- Windows Defender: Built into Windows, it provides basic protection and can detect some spyware.
- AdwCleaner: This tool is specifically designed to remove adware and unwanted programs.
Removing Spyware: Step-by-Step Guide
Once you've identified spyware on your computer, it's vital to remove it. Follow these steps:
Step 1: Disconnect from the Internet
To prevent the spyware from transmitting data, disconnect your computer from the internet.
Step 2: Boot in Safe Mode
Restart your computer and boot into Safe Mode. This limits the number of processes running, making it easier to remove spyware.
Step 3: Run a Full Malware Scan
Use the malware detection tool of your choice to run a full scan. Follow the prompts to remove any detected threats.
Step 4: Delete Temporary Files
Deleting temporary files can help remove remnants of spyware. Use tools like Disk Cleanup or CCleaner.
Step 5: Restore Your System
If the spyware persists, consider restoring your system to a previous state using System Restore.
Preventing Future Spyware Infections
Prevention is key to avoiding spyware infections. Here are some tips:
- Keep Your Software Updated: Regular updates can fix vulnerabilities that spyware exploits.
- Use a Reliable Antivirus: Invest in a good antivirus program that provides real-time protection against malware.
- Be Cautious of Downloads: Avoid downloading software from untrusted sources.
- Educate Yourself: Stay informed about the latest cybersecurity threats and how to avoid them.
Real-World Examples of Spyware Attacks
Understanding real-world spyware incidents can help illustrate the importance of awareness:
Case Study 1: The FinFisher Spyware
FinFisher is a commercial spyware that has been used by governments to monitor citizens. It can access files, record conversations, and track online activity.
Case Study 2: The Pegasus Spyware
Developed by NSO Group, Pegasus has been used to exploit vulnerabilities in smartphones, allowing attackers to access calls, messages, and even turn on the camera.
Expert Insights on Spyware
We consulted cybersecurity experts to gain insights into the spyware landscape:
“Education is the first line of defense against spyware. Users must be aware of the risks and how to protect themselves.” - Jane Doe, Cybersecurity Analyst
Case Studies on Spyware Incidents
Analyzing past spyware incidents can provide valuable lessons:
Case Study 1: The Target Breach
In 2013, Target faced a massive data breach due to malware that infiltrated its systems, leading to the theft of millions of credit card details.
Case Study 2: The Equifax Data Breach
Equifax suffered a data breach in 2017 that exposed sensitive information of 147 million individuals, primarily due to unpatched software vulnerabilities.
FAQs
1. What is the best way to check for spyware?
The best way to check for spyware is to use specialized malware detection tools and perform a thorough system scan.
2. Can spyware be removed completely?
Yes, spyware can be completely removed using reliable malware removal tools and following proper removal procedures.
3. How can I prevent spyware from infecting my computer?
Prevent spyware infections by keeping your software updated, using strong antivirus protection, and being cautious about downloads.
4. Is spyware legal?
While spyware is legal in some contexts, using it to invade someone’s privacy without consent is illegal.
5. What are the signs of a spyware infection?
Signs include slow performance, unexpected pop-ups, unfamiliar programs, and unusual internet activity.
6. Can I detect spyware manually?
Yes, you can check for unusual programs and processes manually, but using specialized tools is more effective.
7. Are there free tools to remove spyware?
Yes, tools like Malwarebytes and AdwCleaner offer free versions that can effectively remove spyware.
8. What should I do if I suspect spyware?
If you suspect spyware, disconnect from the internet, run a malware scan, and remove any detected threats.
9. Can spyware affect my mobile device?
Yes, spyware can also infect mobile devices, compromising personal data and privacy.
10. How often should I check for spyware?
It’s advisable to check for spyware regularly, especially after downloading new software or clicking on suspicious links.
By understanding how to identify, remove, and prevent spyware, you are taking crucial steps towards safeguarding your information and privacy.
Random Reads
- Remove paint acrylic tub
- Remove oil from hardwood floor
- Ultimate guide to whiten grout
- How to print on an envelope using microsoft word
- How to print screen hp
- How to turn off driving mode
- How to turn ipad on
- How to use comment boxes in microsoft word
- How to take apart a picture frame
- How to take a screenshot on a mac complete guide