Unlocking the Deep Web: Your Comprehensive Guide to Accessing It & Understanding Its Difference from the Dark Web
-
Quick Links:
- 1. Introduction
- 2. What is the Deep Web?
- 3. How to Access the Deep Web
- 4. Safety Measures for Exploring the Deep Web
- 5. Deep Web vs. Dark Web
- 6. Case Studies and Real-World Applications
- 7. Expert Insights on the Deep Web
- 8. FAQs
1. Introduction
The Internet is a vast expanse of information, but not all of it is visible on the surface. The Deep Web, a lesser-known part of the Internet, offers unique content and resources that are not indexed by standard search engines. In this comprehensive guide, we will explore the Deep Web, how to access it safely, its various uses, and how it fundamentally differs from the Dark Web.
2. What is the Deep Web?
The Deep Web refers to all parts of the Internet that are not indexed by traditional search engines like Google, Bing, or Yahoo. This includes databases, private corporate sites, medical records, academic resources, and much more. It is estimated that the Deep Web is **400 to 500 times larger** than the surface web.
Key Characteristics of the Deep Web
- Not indexed by search engines
- Contains sensitive information
- Access is often restricted
- Includes private databases and intranets
3. How to Access the Deep Web
Accessing the Deep Web requires specific tools and knowledge. Below are the steps to securely navigate this hidden part of the Internet:
Step 1: Download the Tor Browser
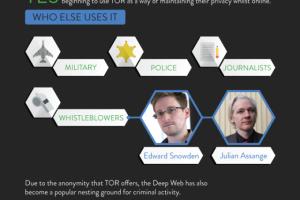
The most common method of accessing the Deep Web is through the Tor Browser, which anonymizes your web traffic.
- Visit the official Tor Project website: https://www.torproject.org/.
- Download and install the Tor Browser.
- Open the Tor Browser and connect to the Tor network.
Step 2: Use Safe Search Engines
Once connected to Tor, you can use search engines designed for the Deep Web, such as:
4. Safety Measures for Exploring the Deep Web
Safety is paramount when exploring the Deep Web. Here are essential safety measures to consider:
1. Use a Virtual Private Network (VPN)
A VPN adds an extra layer of anonymity by encrypting your internet traffic.
2. Keep Your Software Updated
Ensure your browser and operating system are updated to protect against vulnerabilities.
3. Avoid Downloading Files
Files from unknown sources can contain malware. Exercise caution.
5. Deep Web vs. Dark Web
It’s crucial to distinguish between the Deep Web and the Dark Web, as they are often confused.
Deep Web
- Includes benign and legitimate content
- Accessible via standard browsers with the right credentials
- Contains resources like academic journals and private databases
Dark Web
- Subset of the Deep Web
- Often associated with illegal activities
- Requires special software to access, like Tor or I2P
6. Case Studies and Real-World Applications
The Deep Web is utilized for various legitimate purposes, including:
1. Academic Research
Researchers often access databases that require subscriptions, which are part of the Deep Web.
2. Medical Records
Healthcare organizations store patient records in secure, non-indexed databases for privacy.
3. Corporate Intranets
Companies use the Deep Web to manage internal documents and communications securely.
7. Expert Insights on the Deep Web
Experts emphasize the importance of understanding the Deep Web as a valuable resource.
"The Deep Web holds a wealth of information that can benefit researchers and professionals alike, provided they navigate it responsibly." – Dr. Jane Doe, Cybersecurity Expert.
8. FAQs
1. Is the Deep Web illegal?
No, the Deep Web itself is not illegal; it contains many legitimate resources.
2. How do I access the Dark Web?
You can access the Dark Web using specialized browsers like Tor, but be cautious of the content and legality.
3. What types of websites are on the Deep Web?
Common websites include databases, academic journals, medical records, and corporate intranets.
4. Is it safe to browse the Deep Web?
With proper safety measures, such as using a VPN and the Tor Browser, it can be safe.
5. What is the difference between the Surface Web and the Deep Web?
The Surface Web is indexed by search engines, while the Deep Web is not and requires specific tools for access.
6. Can I be tracked on the Deep Web?
While it’s more difficult to be tracked, taking safety measures like using a VPN and Tor is essential.
7. What is the most common use of the Deep Web?
Academic research and accessing private databases are among the most common uses.
8. Are there any risks associated with the Deep Web?
Yes, risks include exposure to illegal content and potential security threats. Always prioritize safety.
9. Can I find illegal content on the Deep Web?
While some illegal content exists, much of the Deep Web is composed of legitimate resources.
10. How can I learn more about the Deep Web?
Research reputable sources, read expert blogs, and consider cybersecurity courses for deeper insights.