How to Detect Remote Access to My Computer: Signs + Expert Tips
-
Quick Links:
- Introduction
- Understanding Remote Access
- Signs of Remote Access
- Expert Tips for Detection
- Protecting Your Computer
- Case Studies
- Conclusion
- FAQs
Introduction
In today's digital age, ensuring the security of your computer is paramount. With the rise of remote access technologies, knowing how to detect unauthorized access to your machine is crucial. This article explores the signs of remote access, expert tips to detect it, and best practices to protect your computer from potential threats.
Understanding Remote Access
Remote access allows users to connect to another computer over the internet or a local network. While it can be useful for legitimate purposes such as remote work, it can also be exploited by cybercriminals. Understanding the mechanisms of remote access is the first step in safeguarding your data.
Types of Remote Access
- Remote Desktop Protocol (RDP): A Microsoft protocol that allows remote access to Windows machines.
- Virtual Network Computing (VNC): A graphical desktop sharing system that allows remote control of another computer.
- Third-party applications: Software like TeamViewer, AnyDesk, or LogMeIn that facilitate remote access.
Signs of Remote Access
Detecting remote access can sometimes be tricky. However, there are several signs that may indicate your computer is being accessed without your permission:
- Unusual Activity: If your mouse moves unexpectedly, or programs open and close without your input, this could indicate remote access.
- New Programs: The appearance of unfamiliar software can be a sign that someone has accessed your computer.
- System Performance Issues: A sudden slowdown in system performance may indicate unauthorized processes running in the background.
- Firewall Alerts: If your firewall is alerting you to unusual outgoing traffic, this could indicate remote access.
- Unrecognized Login Attempts: Check your login history. Any attempts from unknown locations should raise a red flag.
Expert Tips for Detection
To effectively detect remote access, consider the following expert tips:
1. Monitor Active Connections
Use tools like Network Monitor to check for active connections to your computer. Look for any unfamiliar IP addresses.
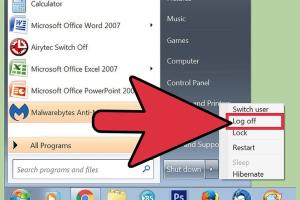
2. Check Task Manager
Open Task Manager (Ctrl + Shift + Esc) and look for any suspicious processes that are running. Research any unfamiliar process names online.
3. Use Security Software
Invest in reputable antivirus and anti-malware software. Programs like Malwarebytes can help identify and remove unauthorized remote access tools.
4. Update Your Software Regularly
Keep your operating system and software up to date to protect against vulnerabilities that could be exploited for unauthorized access.
5. Implement Strong Passwords
Use complex passwords and change them regularly to protect your accounts from unauthorized access.
Protecting Your Computer
After detecting potential remote access, it is essential to take immediate action to secure your computer:
- Disconnect from the Internet: If you suspect unauthorized access, disconnect your computer from the internet to prevent further intrusion.
- Change Passwords: Update your passwords for all accounts, especially those that contain sensitive information.
- Enable Two-Factor Authentication: Whenever possible, enable two-factor authentication for an extra layer of security.
- Audit Installed Programs: Uninstall any unfamiliar or suspicious software.
- Consult a Professional: If you are unsure about the steps to take, consider hiring a cybersecurity professional.
Case Studies
Case Study 1: The Remote Access Trojan
A small business fell victim to a Remote Access Trojan (RAT) that allowed hackers to control their computers remotely. By recognizing the signs early — unusual file access and slow performance — they were able to disconnect their network and seek professional help before significant data loss occurred.
Case Study 2: The Unsecured Remote Desktop
A freelancer used RDP without proper security measures, leading to an unauthorized user accessing sensitive client data. The freelancer learned the importance of strong passwords and firewalls and implemented these measures to prevent future incidents.
Conclusion
Being aware of the signs of remote access and knowing how to detect it is critical for maintaining your computer's security. By following expert tips and taking proactive measures, you can protect your data and ensure your peace of mind in an increasingly digital world.
FAQs
1. What is remote access?
Remote access allows users to connect to another computer or network from a different location, often used for remote work or support.
2. How can I tell if someone is accessing my computer remotely?
Signs include unusual mouse movement, unfamiliar software, and alerts from your firewall.
3. What should I do if I suspect remote access?
Disconnect from the internet, change your passwords, and run a security scan.
4. Can I prevent remote access to my computer?
Yes, by using strong passwords, keeping software updated, and implementing security measures like firewalls.
5. What tools can I use to detect remote access?
Tools like Task Manager, network monitoring software, and antivirus programs can help detect unauthorized access.
6. Is remote access dangerous?
It can be if exploited by unauthorized users, leading to data breaches and other security issues.
7. How do I secure my network from remote access threats?
Use strong passwords, enable two-factor authentication, and configure your firewall properly.
8. What is a Remote Access Trojan (RAT)?
A RAT is a malicious software that allows hackers to control your computer remotely without your consent.
9. How often should I check for remote access?
Regularly monitor your system and network connections, especially if you notice any unusual activity.
10. Where can I learn more about computer security?
Websites like the Cybersecurity & Infrastructure Security Agency provide valuable resources on cybersecurity.
For more information on cybersecurity, you can refer to these authoritative sources:
- Cybersecurity & Infrastructure Security Agency
- NIST Cybersecurity Framework
- Kaspersky on Remote Access Security
Random Reads