Mastering Firewall Security: A Comprehensive Guide to Checking Your Firewall Settings
-
Quick Links:
- Introduction
- What is a Firewall?
- Importance of Firewall Settings
- Types of Firewalls
- How to Check Your Firewall Settings
- Checking Windows Firewall Settings
- Checking Mac Firewall Settings
- Checking Linux Firewall Settings
- Checking Router Firewall Settings
- Common Firewall Issues
- Best Practices for Firewall Management
- Case Studies in Firewall Security
- Expert Insights on Firewall Settings
- Conclusion
- FAQs
Introduction
In today's digital age, cybersecurity is paramount. One of the first lines of defense against cyber threats is a properly configured firewall. A firewall acts as a barrier between your internal network and external threats, controlling the incoming and outgoing network traffic based on predetermined security rules. Knowing how to check your firewall settings is essential for maintaining network security.What is a Firewall?
A firewall is a network security device that monitors and controls incoming and outgoing network traffic based on security rules. Firewalls can be hardware-based, software-based, or a combination of both. They help protect networks from unauthorized access and attacks, making them a critical component of cybersecurity.Importance of Firewall Settings
Properly configured firewall settings are vital to ensure that your network remains secure. Misconfigured settings can leave vulnerabilities open to attackers, leading to data breaches and loss of sensitive information. Regularly checking your firewall settings helps maintain optimal protection and adapts to evolving cybersecurity threats.Types of Firewalls
Understanding the different types of firewalls can help you choose the right protection for your needs. Here are the most common types:- Packet-Filtering Firewalls: These examine packets of data and allow or block them based on user-defined rules.
- Stateful Inspection Firewalls: These track active connections and determine which packets to allow based on the state of the connection.
- Proxy Firewalls: These act as intermediaries between a user and the internet, hiding the user's IP address and filtering traffic.
- Next-Generation Firewalls (NGFW): These include additional features like intrusion prevention systems (IPS), encrypted traffic inspection, and deep packet inspection.
How to Check Your Firewall Settings
Checking your firewall settings is crucial for maintaining network security. Below are step-by-step guides for checking firewall settings on various platforms.Checking Windows Firewall Settings
1. **Open Control Panel**: Click on the Start menu and type "Control Panel" in the search box. 2. **Navigate to System and Security**: Click on "System and Security." 3. **Select Windows Defender Firewall**: Click on "Windows Defender Firewall." 4. **Check Firewall Status**: Here, you can see if the firewall is on or off. You can also adjust settings by clicking on "Allow an app or feature through Windows Defender Firewall." 5. **Advanced Settings**: For detailed settings, click on "Advanced settings" on the left panel. This will open the Windows Firewall with Advanced Security window.Checking Mac Firewall Settings
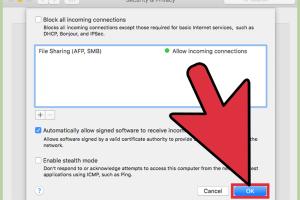
1. **Open System Preferences**: Click on the Apple icon in the top left corner and select "System Preferences." 2. **Click on Security & Privacy**: Choose "Security & Privacy" from the options. 3. **Select the Firewall Tab**: Click on the "Firewall" tab to check the status. 4. **Enable Firewall**: If the firewall is off, you can turn it on by clicking "Turn On Firewall." 5. **Firewall Options**: Click on "Firewall Options" to configure which applications can accept incoming connections.Checking Linux Firewall Settings
1. **Open Terminal**: Access the terminal on your Linux system. 2. **Check UFW Status**: Type `sudo ufw status` to see the current status of the firewall. 3. **Enable/Disable Firewall**: You can enable it using `sudo ufw enable` or disable it with `sudo ufw disable`. 4. **List Rules**: To see the rules that are currently set, use `sudo ufw status verbose`.Checking Router Firewall Settings
1. **Access Router Settings**: Open a web browser and enter your router's IP address (commonly 192.168.1.1 or 192.168.0.1). 2. **Log In**: Enter your router's username and password. 3. **Navigate to Firewall Settings**: Look for a section titled "Firewall," "Security," or "Advanced." 4. **Check Firewall Status**: Here, you can enable or disable the firewall, as well as configure specific settings.Common Firewall Issues
Understanding common issues can help you troubleshoot effectively. Here are some frequent problems: - **Firewall Blocking Legitimate Traffic**: Sometimes, firewalls may incorrectly block safe applications. Adjust settings or add exceptions for trusted programs. - **Performance Issues**: An overly restrictive firewall can slow down your network. Regularly review and optimize your firewall rules. - **Misconfigurations**: Incorrect settings can lead to vulnerabilities. Regular audits of your firewall rules are essential.Best Practices for Firewall Management
To maintain optimal security, follow these best practices: - **Regular Updates**: Keep your firewall software updated to protect against new threats. - **Conduct Regular Audits**: Periodically review your firewall settings and rules to ensure they align with your current security needs. - **User Training**: Educate users on the importance of firewall settings and secure practices. - **Implement Logging and Monitoring**: Enable logging features to monitor and analyze network traffic for unusual activity.Case Studies in Firewall Security
1. **Target Data Breach (2013)**: Target's failure to adequately configure its firewalls allowed attackers to access over 40 million credit card numbers. This incident underscores the importance of regular firewall audits. 2. **Equifax Data Breach (2017)**: This breach, which exposed 147 million people's information, was partially due to misconfigured firewalls. Regular checks could have prevented this incident.Expert Insights on Firewall Settings
According to cybersecurity expert Bruce Schneier, "Firewalls are your first line of defense. However, they are not a silver bullet. Regular checks and updates are essential to keeping your network secure."Conclusion
In conclusion, knowing how to check your firewall settings is essential for maintaining cybersecurity. Properly configured firewalls protect your network from unauthorized access and cyber threats. Regular audits and updates will help ensure your firewall remains effective against evolving threats.FAQs
1. How often should I check my firewall settings?
It is recommended to check your firewall settings at least once a month or whenever you install new software or devices.
2. Can I use multiple firewalls on my system?
While it is possible to use multiple firewalls, it can lead to conflicts. It's advisable to use either a hardware firewall or a software firewall, not both.
3. What should I do if my firewall is blocking a necessary application?
You can add an exception for that application in your firewall settings to allow it to operate without restrictions.
4. What is the difference between hardware and software firewalls?
Hardware firewalls are standalone devices that protect the entire network, while software firewalls are installed on individual devices to protect them specifically.
5. How can I improve my firewall security?
Regularly update your firewall software, conduct audits, and educate users on secure practices to improve security.
6. Are firewalls enough for network security?
No, firewalls are a critical component, but they should be part of a multi-layered security strategy that includes antivirus software and security protocols.
7. Can I temporarily disable my firewall?
While it is possible to disable your firewall, it is not recommended as it exposes your network to potential threats. Always enable it after necessary changes.
8. What is a next-generation firewall?
A next-generation firewall (NGFW) includes features such as intrusion prevention systems (IPS), application awareness, and deep packet inspection for enhanced security.
9. How can I reset my firewall settings?
You can reset your firewall settings to default through the firewall management menu on your operating system or device.
10. Should I hire a professional for firewall configuration?
If you're unsure about configuring your firewall, hiring a cybersecurity professional can ensure optimal security for your network.
Random Reads
- How to fix deep scratches in wood
- How to fix faded plastic
- Wordpress api key guide
- Windows xp repair install
- How to copy a table from word
- How to apply thermal paste
- How to apply tung oil
- How to connect macbook pro to printer
- 4 easy ways to download install mozilla firefox
- How to identify a refurbished iphone