Cybersecurity
Ultimate Guide to Safeguarding Your Computer with Antivirus Software

Discover how to protect your computer with antivirus software. Learn tips, tricks, and essential insights to ensure your digital safety. Read More »
Ultimate Guide to Defending Against a Ram: Strategies & Insights

Discover effective strategies for defending against a ram attack. Learn techniques, tools, and expert insights to enhance your security. Read More »
Ultimate Guide to Effective Password Management: Secure Your Digital Life

Learn how to manage your passwords effectively with this comprehensive guide. Tips, tools, and strategies for better security. Read More »
Creating Memorable Passwords: The Ultimate Guide to Password Management

Discover how to create memorable passwords that enhance your security without the hassle of forgetting them. Read More »
Mastering the Attrib Command: A Guide to Locating Hidden Viruses on Your System

Learn how to locate viruses using the Attrib command effectively. Discover step-by-step methods and expert insights in this comprehensive guide. Read More »
Definitive Guide on How to Report Hackers: Your Step-by-Step Resource

Learn how to report hackers effectively with our comprehensive guide. Get tips, case studies, and expert advice on cybersecurity reporting. Read More »
Identifying Trojan Horse Infections: A Comprehensive Guide

Discover how to tell if your computer is infected by a Trojan horse with our comprehensive guide. Learn symptoms, detection, and prevention. Read More »
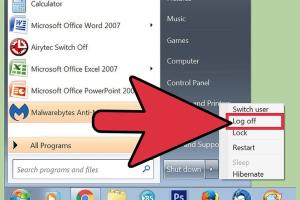
Stay Safe From Hackers: Essential Strategies for Protecting Your Accounts & Devices

Learn effective strategies to protect your accounts and devices from hackers. Stay safe with expert tips and best practices. Read More »
Yahoo Account Hacked? Here’s Your Comprehensive Recovery Guide

Discover what to do if your Yahoo account is hacked. Step-by-step recovery guide, expert tips, and FAQs to secure your account. Read More »
Mastering Password Security: The Ultimate Guide to Creating Strong Passwords

Learn how to create a secure password with our comprehensive guide. Discover tips, tools, and best practices for password security. Read More »
Mastering GPG: A Comprehensive Guide to Verifying GPG Signatures
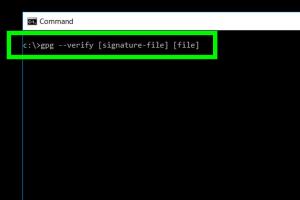
Learn how to verify a GPG signature with our in-depth guide. Step-by-step instructions, expert insights, and real-world examples await! Read More »
Unlocking Shodan: A Comprehensive Guide to Using the Internet's Search Engine for Devices
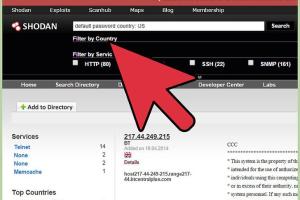
Learn how to effectively use Shodan to discover devices connected to the internet. Step-by-step guide, tips, and expert insights await! Read More »
Mastering PGP: A Comprehensive Guide to Verifying PGP Signatures
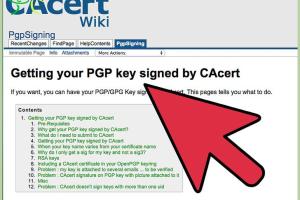
Learn how to verify PGP signatures with our detailed step-by-step guide, tips, and expert insights to enhance your digital security. Read More »
Identifying Cyber Intrusions: How to Know If You've Been Hacked

Uncover warning signs of a cyber hack. Learn how to detect if you've been hacked with our comprehensive guide filled with expert insights. Read More »
Identifying Spyware on Your Computer: A Comprehensive Guide
Learn how to identify if your computer has spyware with our comprehensive guide. Protect your privacy and data today. Read More »
Uncovering the Truth: How to Identify Who Hacked Your Yahoo Email Account

Discover how to find out who hacked your Yahoo email with our comprehensive guide, including tips, tools, and recovery steps. Read More »
How to Detect Pegasus Spyware on Your Smartphone: A Comprehensive Guide

Learn how to check your smartphone for Pegasus spyware with our comprehensive guide. Stay secure and informed with expert tips and tools. Read More »
Mastering Firewall Security: A Comprehensive Guide to Checking Your Firewall Settings
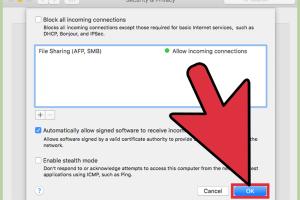
Learn how to check your firewall settings with our in-depth guide, ensuring optimal protection for your network and devices. Read More »
Mastering the Art of Hacking: A Comprehensive Guide to Becoming a Hacker

Learn how to become a hacker with this comprehensive guide, covering skills, tools, and ethical hacking practices. Read More »
Ultimate Guide to Removing Trojan Horses: Protect Your Computer Today
Learn how to effectively remove Trojan horses from your computer with our comprehensive guide. Protect your data now! Read More »
Crafting the Ultimate Secure Password Hint: A Comprehensive Guide
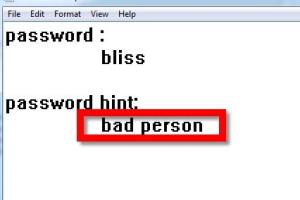
Learn how to create a secure password hint that enhances your digital safety. Protect your accounts effectively with our comprehensive guide. Read More »
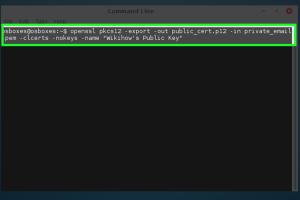
Mastering Certificate Public Key Export from Chrome: A Comprehensive Guide

Learn how to easily export a certificate public key from Chrome with our detailed step-by-step guide. Perfect for cybersecurity and IT professionals. Read More »
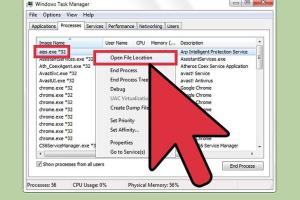
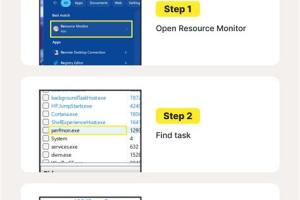
How to Detect Remote Access to My Computer: Signs + Expert Tips
Learn how to detect remote access to your computer with expert tips and signs. Stay secure and protect your data! Read More »
Mastering Cybersecurity: How to Avoid Becoming a Script Kiddie

Learn how to avoid becoming a script kiddie in cybersecurity with expert tips, guides, and insights. Empower your skills today! Read More »
Effective Strategies to Remove Worm Viruses from Your Computer

Learn how to effectively remove worm viruses from your computer with our comprehensive guide, including step-by-step instructions and expert tips. Read More »
Mastering Certificate Authority: Become Your Own CA Today
Learn how to be your own Certificate Authority (CA) with our comprehensive guide. Manage SSL certificates like a pro! Read More »
8 Essential Tips to Become a Qualified and Professional Ethical Hacker

Discover 8 essential tips to become a qualified and professional ethical hacker. Learn skills, strategies, and resources to excel in cybersecurity. Read More »
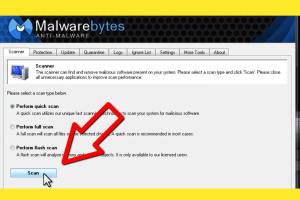
Ultimate Guide: How to Detect and Remove Malware From Your Computer Safely and Effectively
Learn how to detect and remove malware from your computer with this comprehensive guide. Protect your system today! Read More »
Ultimate Guide to Detecting and Removing Keyloggers Safely

Learn how to detect and remove keyloggers effectively. Protect your privacy with our comprehensive guide on keylogger detection and removal. Read More »
Mastering Hackthissite.org: Your Ultimate Guide to Beating Basic Missions
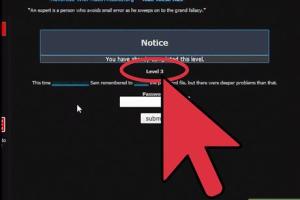
Unlock the secrets to conquering Hackthissite.org Basic Missions with in-depth strategies and expert insights. Read More »