Cybersecurity
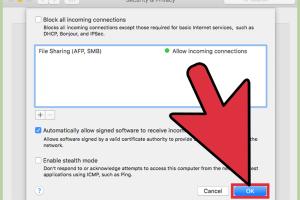
Ultimate Guide to Routing All Network Traffic Through the Tor Network

Learn how to route all your network traffic through the Tor network for enhanced privacy and security. Step-by-step guide included. Read More »
How to Turn Off Microsoft Defender in Windows 10: Step-by-Step Guide

Learn how to temporarily or permanently turn off Microsoft Defender in Windows 10 with this comprehensive step-by-step guide. Read More »
Stay Safe From Hackers: Essential Strategies for Protecting Your Accounts & Devices

Learn effective strategies to protect your accounts and devices from hackers. Stay safe with expert tips and best practices. Read More »
The Beginner's Handbook: Unlocking the Secrets of Ethical Hacking
Dive into ethical hacking with our ultimate beginner's guide. Learn techniques, tools, and strategies for success in the cybersecurity field. Read More »
Definitive Guide on How to Report Hackers: Your Step-by-Step Resource

Learn how to report hackers effectively with our comprehensive guide. Get tips, case studies, and expert advice on cybersecurity reporting. Read More »
Ultimate Guide: How to Reset Your Router Password for Enhanced Security

Learn how to reset your router password effectively with step-by-step guides and expert insights to enhance your home network security. Read More »
How to Effectively Report a Bank of America Phishing Email: A Step-by-Step Guide
Learn how to report a Bank of America phishing email effectively with our comprehensive guide. Protect your personal information today. Read More »
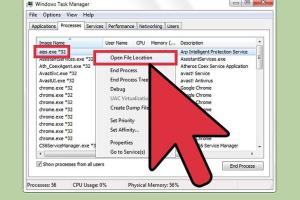
Identifying Cyber Intrusions: How to Know If You've Been Hacked

Uncover warning signs of a cyber hack. Learn how to detect if you've been hacked with our comprehensive guide filled with expert insights. Read More »
Identifying Trojan Horse Infections: A Comprehensive Guide

Discover how to tell if your computer is infected by a Trojan horse with our comprehensive guide. Learn symptoms, detection, and prevention. Read More »
Ultimate Guide to Safeguarding Your Computer with Antivirus Software

Discover how to protect your computer with antivirus software. Learn tips, tricks, and essential insights to ensure your digital safety. Read More »
Smart Strategies: How to Reply to a Text Scammer, Report & Prevent Spam
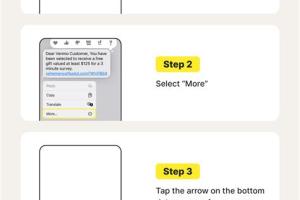
Learn how to effectively respond to text scammers, report them, and prevent spam with our comprehensive guide. Stay safe! Read More »
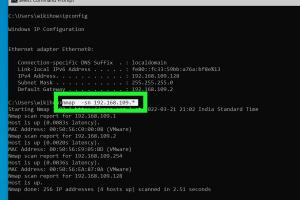
Discovering Hidden Locations: A Comprehensive Guide on How to Trace an IP Address
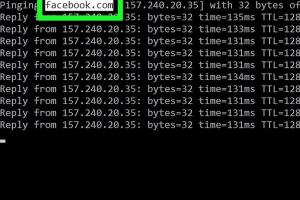
Learn how to trace an IP address effectively. Step-by-step guide with tools, techniques, and expert insights for beginners and professionals. Read More »
Mastering Password Security: The Ultimate Guide to Creating Strong Passwords

Learn how to create a secure password with our comprehensive guide. Discover tips, tools, and best practices for password security. Read More »
Essential Guide to Preventing Easy Installation of Virtual Machines in VMware Workstation

Learn how to effectively prevent the easy installation of virtual machines in VMware Workstation with detailed strategies and insights. Read More »
2 Simple Ways to Manually Remove Adware from Your Computer
Discover 2 easy methods to manually remove adware from your computer and regain control over your device. Read More »
Mastering Online Investigations: How to Use Your Computer to Investigate People

Learn effective methods to use your computer for investigating people, ensuring privacy and ethical considerations are met. Read More »
Mastering GPG: A Comprehensive Guide to Verifying GPG Signatures
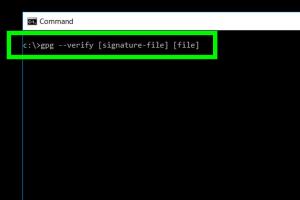
Learn how to verify a GPG signature with our in-depth guide. Step-by-step instructions, expert insights, and real-world examples await! Read More »
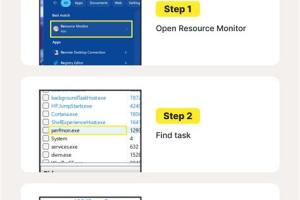
Mastering the Attrib Command: A Guide to Locating Hidden Viruses on Your System

Learn how to locate viruses using the Attrib command effectively. Discover step-by-step methods and expert insights in this comprehensive guide. Read More »
Mastering the Hacker Aesthetic: How to Look Like a Professional Computer Hacker

Discover how to master the hacker aesthetic and look like a professional computer hacker with style, skills, and techniques. Read More »
Ultimate Guide to Removing Viruses: Step-by-Step Strategies for PC & Mac

Learn how to effectively remove viruses from your devices with expert strategies and step-by-step guides. Protect your tech today! Read More »
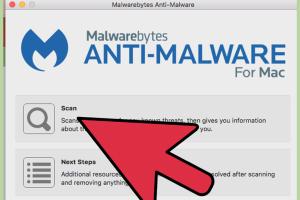
Identifying Spyware on Your Computer: A Comprehensive Guide
Learn how to identify if your computer has spyware with our comprehensive guide. Protect your privacy and data today. Read More »
10 Proven Ways to Stop Online Tracking and Protect Your Privacy
![]()
Discover effective strategies to prevent online tracking and safeguard your privacy. Learn how to reclaim control over your digital footprint. Read More »
11 Essential Ways to Ensure a File’s Safety Before Downloading
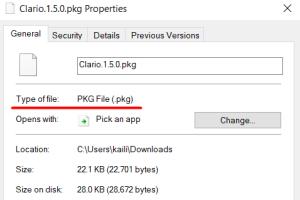
Learn how to determine if a file is safe to download with these 11 essential tips. Protect your device and data from malware! Read More »
Mastering the Art of Hacking: A Comprehensive Guide to Becoming a Hacker

Learn how to become a hacker with this comprehensive guide, covering skills, tools, and ethical hacking practices. Read More »
Ultimate Guide to Defending Against a Ram: Strategies & Insights

Discover effective strategies for defending against a ram attack. Learn techniques, tools, and expert insights to enhance your security. Read More »
How to Detect Pegasus Spyware on Your Smartphone: A Comprehensive Guide

Learn how to check your smartphone for Pegasus spyware with our comprehensive guide. Stay secure and informed with expert tips and tools. Read More »
Ultimate Guide: How to Detect and Remove Malware From Your Computer Safely and Effectively
Learn how to detect and remove malware from your computer with this comprehensive guide. Protect your system today! Read More »
Ultimate Guide to Detecting and Removing Keyloggers Safely

Learn how to detect and remove keyloggers effectively. Protect your privacy with our comprehensive guide on keylogger detection and removal. Read More »
Step-by-Step Guide: Downloading and Installing Avast! Free Antivirus

Learn how to download and install Avast! Free Antivirus with this comprehensive guide. Step-by-step instructions, tips, and FAQs included. Read More »
Unlocking the Secrets: How to Get a MAC Address from an IP Remotely
Learn how to remotely obtain a MAC address from an IP address with step-by-step guides, case studies, and expert insights. Read More »
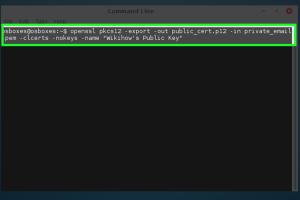
Mastering Certificate Public Key Export from Chrome: A Comprehensive Guide

Learn how to easily export a certificate public key from Chrome with our detailed step-by-step guide. Perfect for cybersecurity and IT professionals. Read More »
Mastering Certificate Authority: Become Your Own CA Today
Learn how to be your own Certificate Authority (CA) with our comprehensive guide. Manage SSL certificates like a pro! Read More »
Mastering Online Anonymity: 15 Essential Tricks for Ultimate Privacy

Discover 15 essential tricks to maintain your privacy online and navigate the web anonymously. Safeguard your digital footprint today! Read More »
Mastering Security: Your Comprehensive Guide to Staying Safe in a Digital World

Explore essential tips and strategies on how to be secure in today’s digital landscape with our in-depth guide. Stay safe online and offline. Read More »
Unlocking the Digital Realm: A Complete Guide to Becoming a Teen Hacker

Discover how to become a teen hacker with our comprehensive guide. Learn skills, tools, and ethical hacking practices for a secure future. Read More »
Ultimate Guide: How to Change the Root Password in Linux Easily
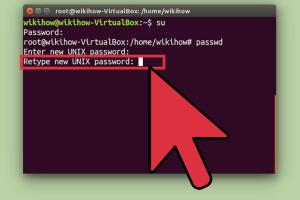
Learn how to effectively change the root password in Linux with this comprehensive guide. Step-by-step instructions and expert insights included. Read More »
Mastering Firewall Security: A Comprehensive Guide to Checking Your Firewall Settings
Learn how to check your firewall settings with our in-depth guide, ensuring optimal protection for your network and devices. Read More »
Effective Strategies to Remove Worm Viruses from Your Computer

Learn how to effectively remove worm viruses from your computer with our comprehensive guide, including step-by-step instructions and expert tips. Read More »
Unlocking the Deep Web: Your Comprehensive Guide to Accessing It & Understanding Its Difference from the Dark Web
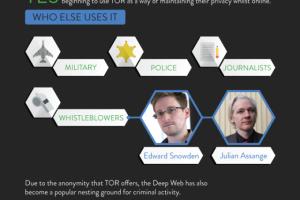
Explore our in-depth guide to the Deep Web, how to access it safely, and how it contrasts with the Dark Web. Read More »
How to Block a Program from Accessing the Internet Using Windows Firewall
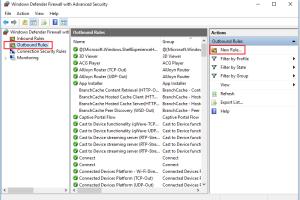
Learn how to effectively block any program from accessing the internet through Windows Firewall with this comprehensive guide. Read More »
Mastering Cybersecurity: How to Avoid Becoming a Script Kiddie

Learn how to avoid becoming a script kiddie in cybersecurity with expert tips, guides, and insights. Empower your skills today! Read More »
Top Strategies to Prevent Hacking on Roblox: Your Ultimate Guide

Learn effective strategies to protect your Roblox account from hacks. Discover tips, insights, and expert advice to stay safe online. Read More »
Mastering Hackthissite.org: Your Ultimate Guide to Beating Basic Missions
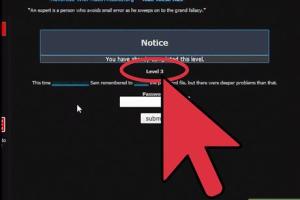
Unlock the secrets to conquering Hackthissite.org Basic Missions with in-depth strategies and expert insights. Read More »
Mastering Free Software Hacking: Your Ultimate Guide to Becoming a Software Hacker
Unlock your potential by learning how to become a free software hacker with our detailed guide. Start your journey today! Read More »
8 Essential Tips to Become a Qualified and Professional Ethical Hacker

Discover 8 essential tips to become a qualified and professional ethical hacker. Learn skills, strategies, and resources to excel in cybersecurity. Read More »