Data protection
Phone Stolen? Comprehensive Guide to Deactivate and Delete Your Data

Lost your phone? Learn how to deactivate it and delete your data with our comprehensive guide. Protect your privacy now! Read More »
Safe Computer Practices: A Comprehensive Guide to Working Securely Online

Discover essential tips and strategies for working on a computer safely, including ergonomics, cybersecurity, and best practices. Read More »
Unlocking BitLocker Encrypted Drives via Command Prompt: A Comprehensive Guide
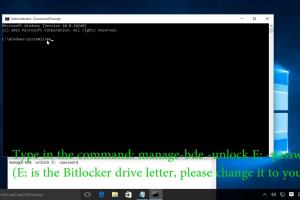
Learn how to unlock BitLocker encrypted drives using Command Prompt with this step-by-step guide, including tips and troubleshooting. Read More »
How to Create Invisible Files: A Comprehensive Guide
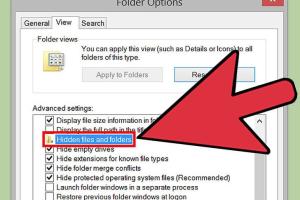
Discover step-by-step methods to create invisible files on various platforms, ensuring your data remains private and secure. Read More »
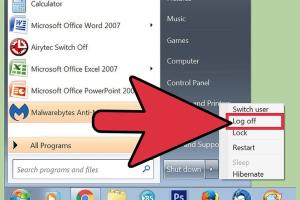
Ultimate Guide: How to Securely Lock Your PC and Mac Without a Password

Learn how to lock your computer with or without a password on PC and Mac in this comprehensive guide. Secure your data now! Read More »
Identifying Spyware on Your Computer: A Comprehensive Guide
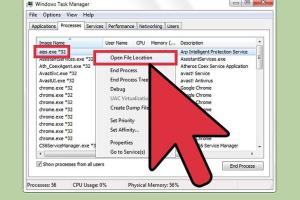
Learn how to identify if your computer has spyware with our comprehensive guide. Protect your privacy and data today. Read More »
Steganography Simplified: How to Hide Files in Image Files Securely
Learn how to hide files in image files using steganography techniques. Secure your data with our step-by-step guide and expert insights. Read More »
Ultimate Guide: How to Lock a Folder Using a Batch File for Enhanced Security
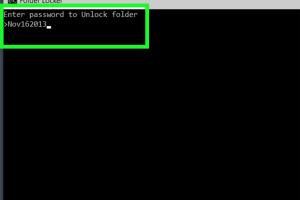
Discover how to lock a folder using a batch file with our step-by-step guide. Secure your data easily and efficiently. Read More »
Mastering File Concealment: How to Hide Files in Windows Using CMD
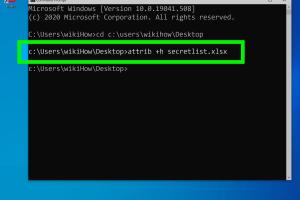
Learn how to hide files in Windows using CMD with this comprehensive guide. Step-by-step instructions and expert tips included. Read More »
Top 10 Proven Strategies to Keep Your Address Private in 2023
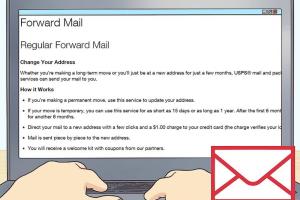
Discover effective strategies to keep your address private and protect your personal information online and offline. Read More »
Mastering Online Anonymity: 15 Essential Tricks for Ultimate Privacy

Discover 15 essential tricks to maintain your privacy online and navigate the web anonymously. Safeguard your digital footprint today! Read More »
Ultimate Guide to Safeguarding Your Email Account from Hackers

Learn essential strategies to protect your email account from hackers. Safeguard your personal data with our comprehensive guide. Read More »
Ultimate Guide: How to Wipe a Computer Safely and Effectively
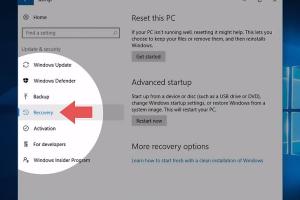
Learn how to wipe a computer safely with our comprehensive guide. Step-by-step instructions, FAQs, and expert tips to ensure data security. Read More »
10 Proven Ways to Stop Online Tracking and Protect Your Privacy
![]()
Discover effective strategies to prevent online tracking and safeguard your privacy. Learn how to reclaim control over your digital footprint. Read More »
Ultimate Guide to Safeguarding Your Computer with Antivirus Software

Discover how to protect your computer with antivirus software. Learn tips, tricks, and essential insights to ensure your digital safety. Read More »
Ultimate Guide: How to Protect Electronics from an Electromagnetic Pulse
Learn effective strategies to safeguard your electronics from electromagnetic pulse (EMP) damage. Expert tips and practical solutions await! Read More »
Step-by-Step Guide to Disable Web & App Activity for Your Google Account
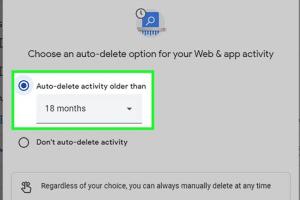
Learn how to disable Web & App Activity on Google for enhanced privacy with our step-by-step guide. Protect your data today! Read More »
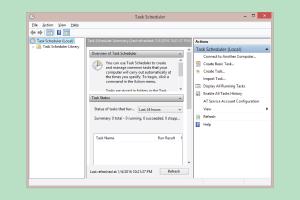
How to Detect Remote Access to My Computer: Signs + Expert Tips
Learn how to detect remote access to your computer with expert tips and signs. Stay secure and protect your data! Read More »
Ultimate Guide to Safely Destroying Floppy Disks: Methods, Tips & Best Practices
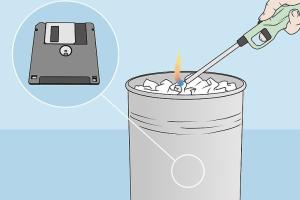
Learn effective and safe methods to destroy floppy disks and protect your data. Step-by-step guide, FAQs, and expert insights included. Read More »
Ultimate Guide: How to Securely Back Up Email Files in Mozilla Thunderbird
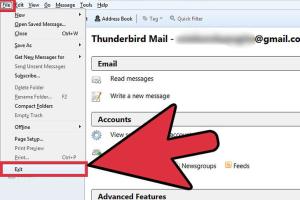
Learn how to back up email files in Mozilla Thunderbird with our comprehensive guide. Protect your data with easy steps! Read More »
Ultimate Guide: How to Effectively Destroy a SIM Card Safely and Securely
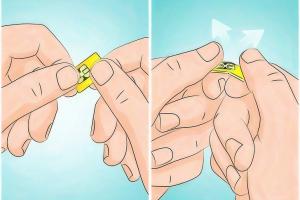
Learn the safest and most effective methods to destroy a SIM card and protect your personal information. Read More »
Essential Guide to Backing Up Your Mac: Secure Your Data Efficiently

Learn how to back up your Mac safely and efficiently with our comprehensive guide. Protect your data today! Read More »
Ultimate Guide to Defending Against a Ram: Strategies & Insights

Discover effective strategies for defending against a ram attack. Learn techniques, tools, and expert insights to enhance your security. Read More »
Ultimate Guide to Deleting Tracking Cookies: Keep Your Privacy Intact
![]()
Learn how to delete tracking cookies and enhance your online privacy with our comprehensive guide. Step-by-step instructions included. Read More »
Ultimate Guide: How to Efficiently Back Up Microsoft Outlook
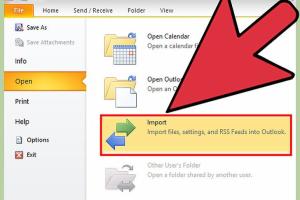
Learn how to back up Microsoft Outlook with our comprehensive guide. Step-by-step instructions and expert tips included. Read More »
Mastering Discretion: The Ultimate Guide to Hiding Porn on Your Computer
Learn effective methods to discreetly hide porn on your computer, ensuring privacy and security with our comprehensive guide. Read More »
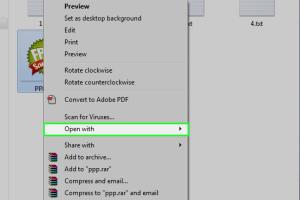
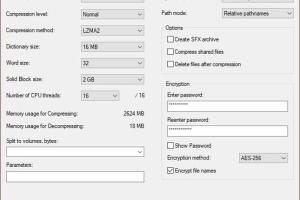
Secure Your Files: A Comprehensive Guide to Adding a Password to RAR Files

Learn how to easily add a password to RAR files for enhanced security. Step-by-step guide with tips and examples. Read More »
Mastering Security: Your Comprehensive Guide to Staying Safe in a Digital World

Explore essential tips and strategies on how to be secure in today’s digital landscape with our in-depth guide. Stay safe online and offline. Read More »
Mastering Privacy: How to Block Cookies in Chrome, Safari, & More

Learn how to block cookies in Chrome, Safari, and other browsers for enhanced online privacy and security. Step-by-step guide included! Read More »
Ultimate Guide on How to Deactivate a Phone: Step-by-Step Instructions

Learn how to deactivate your phone with our ultimate step-by-step guide. Secure your data and make an informed decision today! Read More »
Mastering Encryption: Step-by-Step Guide for Creating Your Own Encryption Algorithm
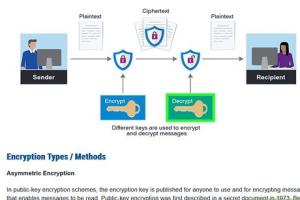
Learn how to create your own encryption algorithm with this comprehensive guide, including examples, insights, and FAQs. Read More »
Ultimate Guide to Clearing the Record of USB Plug-in Equipment
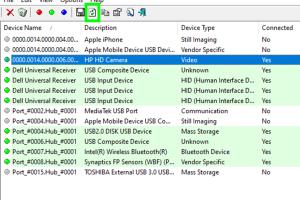
Learn how to effectively clear the record of USB plug-in equipment with our in-depth guide, including step-by-step processes and expert tips. Read More »
A Comprehensive Guide to Securing .Bat Files with Password Protection
Learn how to add password protection to .bat files with this complete guide. Protect your scripts easily and efficiently. Read More »
Effortlessly Clear Your Yahoo Search History: 2 Quick Methods
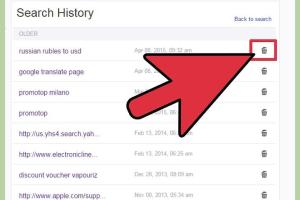
Discover 2 quick methods to delete your Yahoo search history and enhance your online privacy effortlessly. Read More »